Packet Sniffing is a network technique that involves capturing packets of data as they travel across a network. This practice is crucial for network administrators for monitoring and diagnosing network health and security. However, it also raises significant privacy and security concerns when used maliciously.
Exploring the Depths of Packet Sniffing
Packet Sniffing operates by intercepting data packets as they move through a network, allowing the sniffer to see the data’s contents. This can include everything from the destination and source of the packets to the data itself, such as passwords, emails, and other sensitive information. Packet sniffers can be hardware or software-based, and their legality and ethicality depend on the usage context.
Key Features of Packet Sniffing
Packet Sniffing encompasses several key features:
- Data Capture: Ability to capture data packets in real-time.
- Filtering: Tools to filter captured data based on specific criteria.
- Analysis: Capabilities to analyze packet contents for various purposes.
- Stealth: Often operates undetectably by network users and administrators.
Types of Packet Sniffing
| Type | Description |
|---|---|
| Passive Sniffing | Captures packets without altering the network’s state. Used mainly in hub-based networks. |
| Active Sniffing | Involves injecting traffic or manipulating the network to capture data in switch-based networks. |
- ARP Spoofing
- DNS Spoofing
- IP Sniffing
Applications of Packet Sniffing
Packet Sniffing is employed in numerous ways:
- Network Monitoring: Ensuring the network operates smoothly and efficiently.
- Security Analysis: Identifying security vulnerabilities or breaches.
- Troubleshooting: Diagnosing network problems.
- Data Analysis: Gathering insights from network traffic patterns.
Challenges and Solutions in Packet Sniffing
The use of packet sniffing introduces several problems, including privacy concerns, legality issues, and potential misuse by malicious actors. Solutions include:
- Encryption: Encrypting data in transit to prevent unauthorized access.
- Policy and Governance: Implementing strict policies and guidelines for lawful and ethical use.
- Security Measures: Using security tools and practices like firewalls and intrusion detection systems to protect against malicious sniffing.
Comparative Analysis with Similar Technologies
| Feature | Packet Sniffing | Network Monitoring | Intrusion Detection Systems |
|---|---|---|---|
| Purpose | Capture and analyze network packets. | Monitor network health and performance. | Detect and alert on malicious network activities. |
| Method | Passive or active interception. | Continuous monitoring and logging. | Analysis of network traffic for suspicious patterns. |
| Use Case | Security analysis, troubleshooting. | Performance management, troubleshooting. | Security breach detection, prevention. |
Future Directions in Packet Sniffing
Emerging technologies and trends shaping the future of packet sniffing include:
- Enhanced Encryption: Making sniffing more challenging but also pushing for advancements in decryption technologies.
- Artificial Intelligence and Machine Learning: For smarter analysis and identification of patterns in network traffic.
- Internet of Things (IoT): Expanding the scope of sniffing due to the proliferation of connected devices.
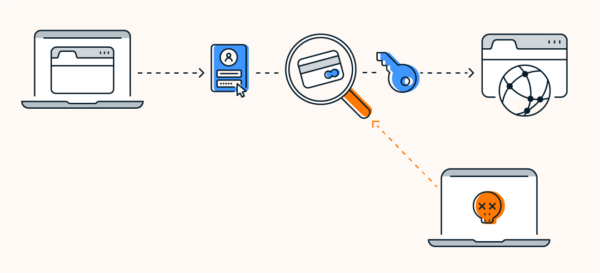
VPNs and Packet Sniffing: A Protective Measure
VPNs (Virtual Private Networks) play a critical role in association with packet sniffing by encrypting data in transit, thus rendering the data captured by sniffers unreadable and useless. This protection is vital in both preventing malicious sniffing and ensuring privacy and security online.
Further Resources on Packet Sniffing
For those interested in delving deeper into packet sniffing, the following resources are invaluable:
- Wireshark: A leading packet analysis tool offering extensive documentation and community support.
- RFC 2616 (Hypertext Transfer Protocol — HTTP/1.1): Offers technical insights into one of the key protocols subject to sniffing.
- SANS Institute: Provides white papers and training on network security, including packet sniffing techniques.
- Cybrary: Offers courses and resources on network security and packet sniffing.
This comprehensive guide to packet sniffing underscores its dual nature as both a critical tool for network management and security and a potential vector for privacy invasion and security breaches. The responsible and ethical use of packet sniffing, coupled with robust security measures like VPNs, is essential in navigating the complex landscape of modern networking.